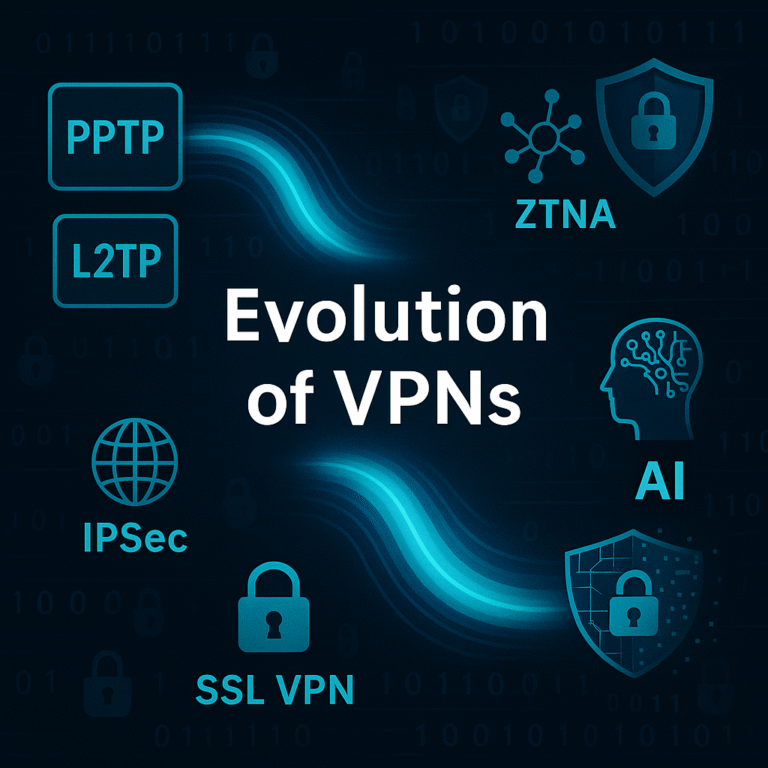
Evolution of VPN: Secure Tunnels to Zero Trust Future
Explore how VPNs evolved from PPTP to Zero Trust and SASE, and discover the future of VPN technology with AI and quantum-safe security.
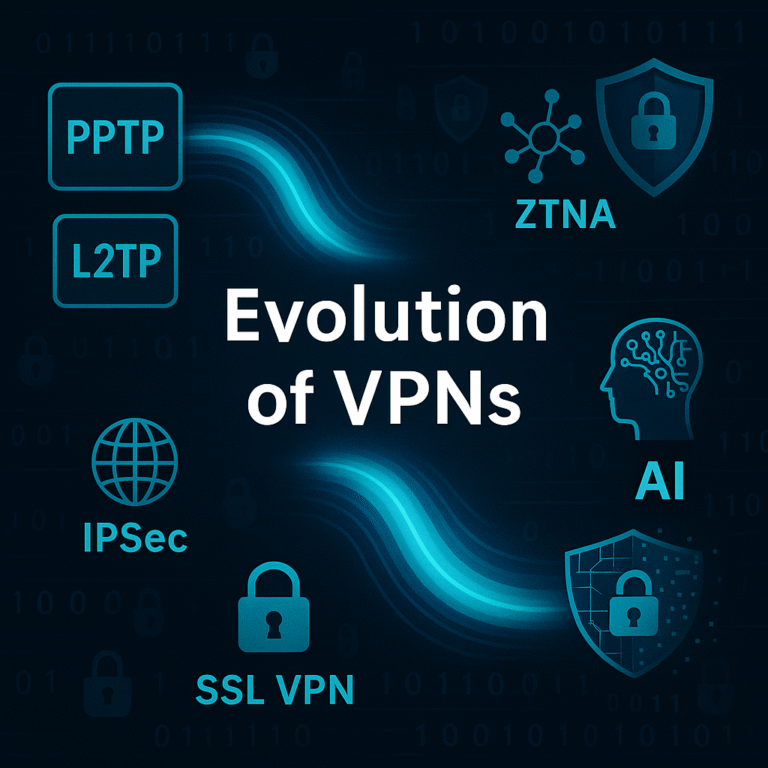
Explore how VPNs evolved from PPTP to Zero Trust and SASE, and discover the future of VPN technology with AI and quantum-safe security.

Learn what a VPN is, why organizations need it, and explore all major VPN types with deep technical insights for security professionals

Introduction to Certified Ethical Hacking (CEH) Certified Ethical Hacking (CEH) is a pivotal credential within the cybersecurity domain that empowers professionals with the expertise to assess and fortify an organization’s security measures. The CEH certification is awarded by the EC-Council…

Discover how network segmentation enhances security in enterprise networks by isolating sensitive data and reducing attack surfaces.

Learn about Linux kernel exploits, their vulnerabilities, and effective mitigation strategies to enhance your cybersecurity defenses.
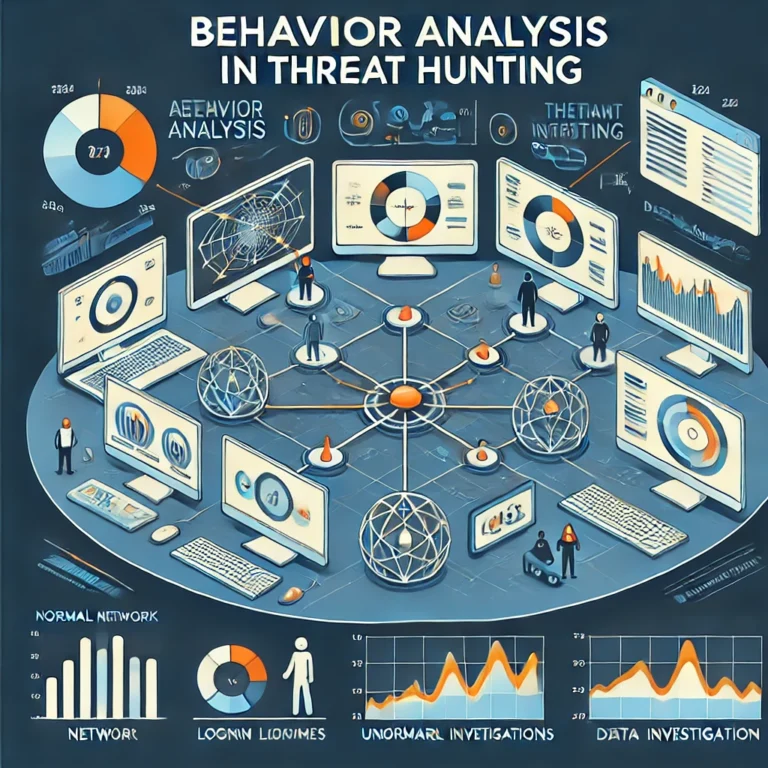
Discover the top threat hunting techniques and tools for 2024, helping cybersecurity experts stay ahead of evolving cyber threats.
Explore how quantum computing is transforming cybersecurity protocols, with a focus on encryption, vulnerabilities, and future challenges.

Explore how to implement Zero Trust architecture in a perimeterless world, ensuring robust cybersecurity for modern enterprises.
Learn the best practices to secure edge computing networks in 2024, focusing on encryption, Zero Trust, and real-time monitoring.

AI-driven cybersecurity in 2024 is proactive, leveraging machine learning and deep learning for advanced threat detection.