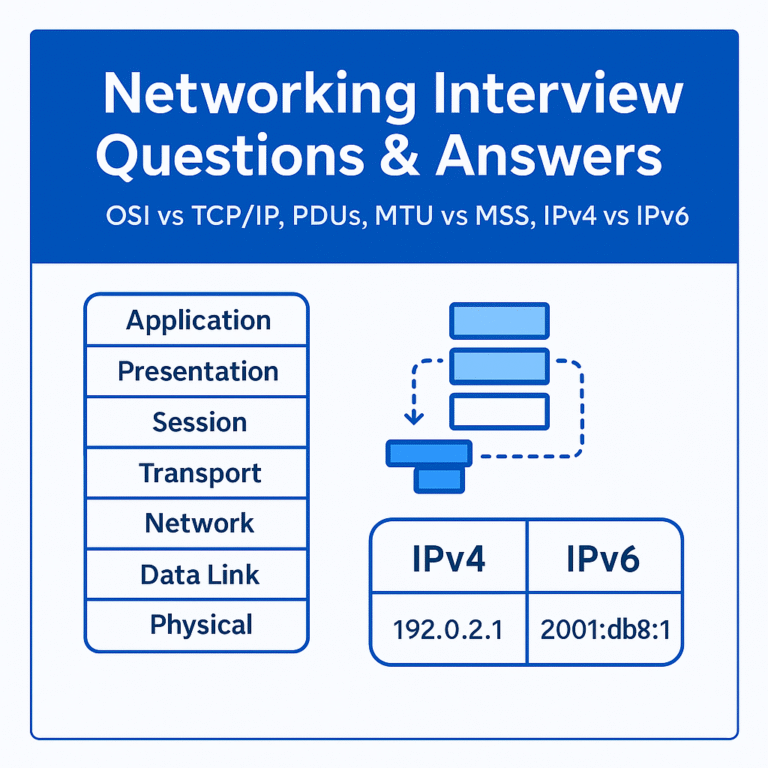
1. What are the OSI Layers?
The OSI model, or Open Systems Interconnection model, is a 7-layer framework that describes how data travels in a network from one device to another. The layers are Physical, Data Link, Network, Transport, Session, Presentation, and Application. Each layer has its own role: the Physical layer is about cables, signals, and hardware; the Data Link layer uses MAC addresses and deals with switches and framing; the Network layer provides logical addressing with IP and handles routing; the Transport layer uses TCP or UDP for segmentation and reliability; the Session layer sets up and manages connections; the Presentation layer translates, compresses, and encrypts data; and finally, the Application layer provides services like HTTP, DNS, FTP, and SMTP. The OSI model is very useful for troubleshooting because you can map problems to layers — for example, if the cable is faulty, it’s a Layer 1 issue, and if a website isn’t loading even though ping works, it’s likely a Layer 7 issue. A simple trick to remember the order is “Please Do Not Throw Sausage Pizza Away.”
2. What is the use of Broadcast IP?
A broadcast IP is used to send a message to all hosts within a network or subnet at once. In any subnet, the first IP is reserved as the network ID, the last IP is reserved as the broadcast address, and all the usable IPs in between are for hosts. When a packet is sent to the broadcast address, every device in that subnet will receive it. This is commonly used in protocols like ARP, where a device asks “who has this IP,” or DHCP Discover, where a client requests an IP address. For example, in the subnet 192.168.1.0/24, the broadcast address is 192.168.1.255. If you send a broadcast ping to this address, all devices in that subnet will respond.
3. What is EtherChannel?
EtherChannel is a technology that allows you to bundle multiple physical links between two switches, or between a switch and a router, into one logical connection. The benefit of EtherChannel is that it increases bandwidth and provides redundancy. For example, if you bundle four 1 Gbps links into an EtherChannel, it acts as a single 4 Gbps logical link. If one of the physical links fails, the traffic is automatically redistributed across the remaining links without causing any disruption. EtherChannel also works well with STP because the group of links is treated as a single interface, so it avoids loops while still providing redundancy. It can be configured using Cisco’s PAgP protocol or the IEEE standard LACP protocol.
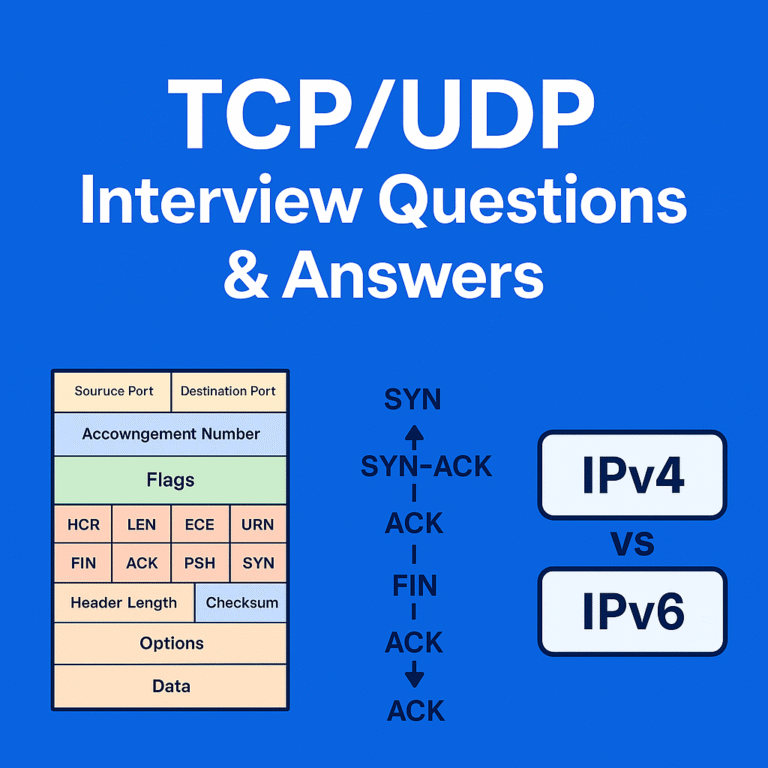
4. TCP Headers and TCP 3-Way Handshake
TCP is a reliable transport layer protocol, and its header contains fields like source and destination port numbers to identify applications, sequence and acknowledgement numbers to ensure ordered delivery, window size for flow control, flags like SYN, ACK, FIN, and RST to manage connections, and checksum for error detection. A very important concept is the TCP 3-way handshake, which is the process of establishing a reliable session. It works in three steps: first the client sends a SYN message to the server to initiate a connection, then the server replies with a SYN-ACK to acknowledge and agree to connect, and finally the client responds with an ACK to complete the process. After this handshake, data transfer can begin reliably. This process ensures that both sides are ready and synchronized before actual data transmission happens.
5. Difference between SSH and Telnet
Telnet and SSH are both used for remote device access, but the key difference is security. Telnet sends all data, including usernames and passwords, in plain text, which makes it highly insecure. SSH, on the other hand, uses encryption to secure the communication, making it the preferred protocol in modern networks. Telnet uses TCP port 23, while SSH uses TCP port 22. In today’s production environments, SSH is always used for secure remote login and device management, whereas Telnet is outdated and is only sometimes used in lab environments for testing.
6. What is Default Route?
A default route is a routing entry that routers use when no specific route is found for a destination in the routing table. It is like a “catch-all” route that ensures packets still have a way out of the network. In IPv4 it is written as 0.0.0.0/0, and in IPv6 it is written as ::/0. The default route is generally configured to point towards the next-hop router, usually an ISP, so that all unknown traffic is forwarded there. For example, in a home router, the default route points to the ISP, so whenever you try to access a website that is not part of your local network, the traffic is automatically forwarded to the ISP and then onto the internet.
7. What is NAT and what is SNAT?
NAT, or Network Address Translation, is the process of modifying IP addresses in packet headers as they pass through a router or firewall. It is mainly used to translate private IP addresses into public IP addresses so that internal devices can access the internet. NAT not only conserves public IPs but also hides internal network details for security. There are different types of NAT: Static NAT, where one private IP is mapped to one public IP; Dynamic NAT, where private IPs are mapped to a pool of public IPs; and PAT or Port Address Translation, where many private IPs share a single public IP using different port numbers, which is the most common form of NAT. SNAT, or Source NAT, is specifically when the source address of a packet is modified, typically when devices in a private network are accessing the internet. For example, when a PC with private IP 192.168.1.10 sends traffic to the internet, the router replaces the source with its public IP, like 203.0.113.5, so the communication works.
8. What is DTP?
DTP, or Dynamic Trunking Protocol, is a Cisco proprietary protocol used by switches to automatically negotiate trunking on a link between two switches. Trunk ports are used to carry multiple VLANs across a link, and DTP helps switches automatically decide whether the link should be a trunk or access link. There are different modes in DTP: Dynamic Desirable actively tries to form a trunk, Dynamic Auto waits passively and will form a trunk only if the other side is Desirable, Trunk forces the interface to be a trunk, and Access forces it to be an access port. For example, if one switch is configured as Dynamic Desirable and the other as Dynamic Auto, they will successfully negotiate and form a trunk automatically.

[…] Questions and Answers – 4 Network Engineer Interview Questions and Answers – 3 Network Engineer Interview Questions with Answers – 2 Network Engineer Interview Questions with Answers Beginner’s Guide to Cybersecurity Careers in […]