1. What is VLAN?
A VLAN, or Virtual Local Area Network, is a logical separation of a physical switch into multiple smaller networks. It allows grouping of devices logically even if they are connected to different switch ports or different switches. The main purposes are to reduce broadcast domains, improve security, and organize traffic efficiently. For example, VLAN 10 can be assigned to HR and VLAN 20 to Finance, so even though they share the same switch, their traffic is separated. VLANs also make networks scalable and easier to manage.
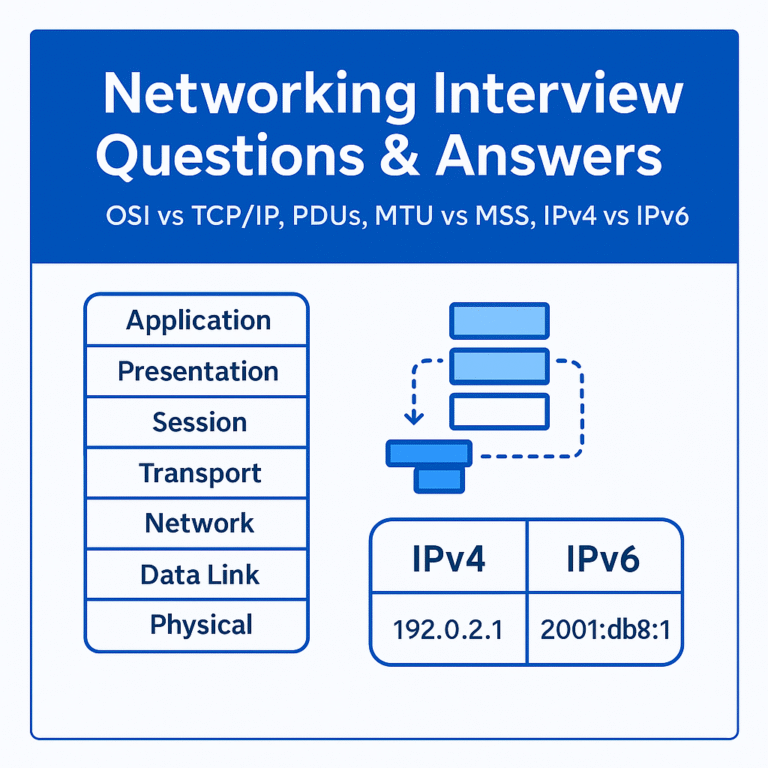
2. Explain the OSI Model.
The OSI, or Open Systems Interconnection Model, is a conceptual 7-layer framework that standardizes how data moves across a network. Each layer has its role:
- Physical – cables, signals, hardware.
- Data Link – MAC addresses, switches, error detection.
- Network – IP addressing, routing.
- Transport – TCP/UDP, segmentation, reliability.
- Session – establishing and ending sessions.
- Presentation – data formatting, encryption, compression.
- Application – protocols like HTTP, DNS, FTP.
This model helps engineers troubleshoot and design networks layer by layer. For example, if ping works but a website doesn’t load, you know the problem is at the Application layer, not the Network layer.
3. What is STP?
STP, or Spanning Tree Protocol, is a Layer 2 protocol designed to prevent loops in switched networks. In modern LANs, redundancy is needed for fault tolerance, but redundant links can cause endless looping frames, known as broadcast storms. STP ensures only one active logical path exists between switches and blocks the rest. This way, redundancy remains but loops are avoided.
4. Why is STP used?
STP is used because without it, redundant links between switches create loops that result in broadcast storms, multiple frame copies, and MAC table instability, which can bring down the entire LAN. STP keeps one link active and others in standby, preventing loops while still allowing redundancy.
5. How does STP avoid loops?
STP avoids loops by following three steps. First, it elects a Root Bridge, which becomes the central reference point. Then, all switches calculate the shortest path to the Root using path cost. Finally, STP places redundant ports into a blocking state so there is only one active path. If the active path fails, STP reactivates a backup path, ensuring both loop prevention and fault tolerance.
6. What is Routing?
Routing is the process of forwarding packets between different networks using routers. While switches work within a LAN using MAC addresses, routers use IP addresses to connect different LANs or connect LANs to the internet. Routers rely on routing tables to choose the best path. For example, when your computer accesses Google, the router checks its table and forwards the packet toward the ISP, which eventually reaches Google’s network.
7. Explain Routing Protocols.
Routing protocols are methods that routers use to exchange information and update their routing tables automatically. They save administrators from manually configuring routes and adapt to network changes quickly. Types include:
- Distance Vector (e.g., RIP) – simple, uses hop count as metric.
- Link State (e.g., OSPF, IS-IS) – routers share complete topology and use algorithms to calculate best paths.
- Path Vector (e.g., BGP) – used on the internet; makes decisions based on policies and attributes.
These protocols make networks more dynamic, scalable, and fault tolerant.
8. Difference between Router and Switch.
A router works at Layer 3, uses IP addresses, and connects different networks, such as your LAN to the internet. A switch works at Layer 2, uses MAC addresses, and connects devices within the same network. Routers choose the best “road” between different cities, while switches decide which “street” inside the city to use. For example, your router connects your office LAN to the ISP, while a switch connects all office PCs together.
9. What is ARP?
ARP, or Address Resolution Protocol, is used to map an IP address to a MAC address inside a LAN. Devices know the destination IP but need the physical MAC to deliver data over Ethernet. Without ARP, devices would not be able to communicate within a local network.
10. Explain the Packet Flow of ARP.
When a device wants to send data to another device in the same subnet, it first checks its ARP table for the MAC address. If it doesn’t find it, it sends a broadcast: “Who has IP X?” The device with that IP replies with its MAC address. The sender stores this mapping in its ARP cache and sends the packet directly. Requests are broadcasts, but replies are unicasts.
11. What are the Different Types of ARP?
- Normal ARP – Maps IP to MAC using request/reply.
- Proxy ARP – A router answers ARP on behalf of another device.
- Gratuitous ARP – A device announces its own IP/MAC, often used in redundancy.
- Reverse ARP (RARP) – Old method to find IP from MAC, rarely used today.
12. What are the Different Types of VLAN?
- Default VLAN – VLAN 1, present on all switches.
- Data VLAN – Used for user-generated traffic.
- Voice VLAN – Special VLAN for VoIP traffic with high priority.
- Management VLAN – Used for remote management of the switch.
- Native VLAN – Used for untagged traffic on trunk ports.
These VLANs help organize traffic and improve performance.
13. Explain Broadcast Domain and Collision Domain.
A broadcast domain is a group of devices that receive a broadcast packet. VLANs and routers separate broadcast domains. A collision domain is where two devices can transmit at the same time, causing collisions. Modern switches eliminate this by giving each port its own collision domain. For example, in old hub networks, the whole hub was one collision domain, but with switches, each port is separate.
14. What is DHCP?
DHCP, or Dynamic Host Configuration Protocol, automatically assigns IP addresses and other network settings like subnet mask, default gateway, and DNS server. This reduces manual work and avoids IP conflicts. Without DHCP, admins would have to configure each device manually.
15. Explain the Process of DHCP.
The DHCP process is known as DORA:
- Discover – The client broadcasts to find a DHCP server.
- Offer – The server offers an available IP.
- Request – The client requests the offered IP.
- Acknowledge – The server confirms the assignment.
This ensures smooth automatic IP distribution.
16. Difference between IPv4 and IPv6.
IPv4 uses 32-bit addressing, supports about 4.3 billion addresses, and often requires NAT. IPv6 uses 128-bit addressing, supports an almost unlimited number of addresses, and removes the need for NAT. IPv6 also has built-in security with IPSec, a simpler header structure, and auto-configuration. For example, an IPv4 address looks like 192.168.1.1, while an IPv6 address looks like 2001:db8::1.
17. Difference between IP Address and MAC Address.
An IP address is a logical Layer 3 identifier that can change depending on the network. It tells where the device is, like a postal address. A MAC address is a physical Layer 2 identifier burned into the network card and unique to each device. It tells who the device is, like a fingerprint. Together, MAC is the identity, and IP is the location.
Tip for Students:
When answering in interviews, always use the flow:
Definition → Why it matters → Example/Analogy.

[…] Interview Questions and Answers – 3 Network Engineer Interview Questions with Answers – 2 Network Engineer Interview Questions with Answers Beginner’s Guide to Cybersecurity Careers in 2025 Mastering CEH v12 & v13: Your […]